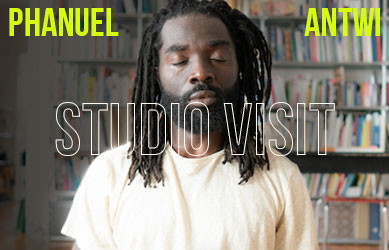
Interview by Nicolas Hausdorf in Berlin; Friday, Oct. 16, 2015
 Portrait of Danja Vasiliev and Julian Oliver, film still from Weise7; photography by Andreas ‘muk’ Haider (tagR.tv)
Portrait of Danja Vasiliev and Julian Oliver, film still from Weise7; photography by Andreas ‘muk’ Haider (tagR.tv)
If you encounter unknown flying objects in the airspace between Frankfurt/Oder and Belarus these days, distrust your first instincts. Aerial balloons with shiny metallic objects floating into the clouds may be neither timid surveillance attempts by a cash-strapped Russian military, the latest Nato or California-based technology giant project for the conquest of space, nor remnants of autumn wedding ceremonies gone awry. What you see may rather be the latest project of Berlin-based artists Julian Oliver and Danja Vasiliev trying to remap an innocent looking autumn sky as an exchange space for encrypted military information. The Deep Sweep is only the latest project of the artists who call themselves critical engineers, according to a manifesto, which since its publication in 2011, has received plenty of attention and has been translated into a more than a dozen of languages. Aside from currently being taught in university classes worldwide (such as at the prestigious MIT), this concept may also serve well in re-thinking a desperately needed more resilient citizenship in a 21st century marked by excess concentrations of corporate and state power.
Oliver and Vasiliev are therefore truly avantgardistic (if such a thing still exists) uniting technological skill, a democratic and transparent DIY ethos, a healthy dose of subversiveness all with spiked with some non-negligible aesthetic surplus value. Their works render comprehensible today’s oftentimes invisible infrastructures of control, always in homage to the popular hacker maxim architecture matters: an ideological immune system booster of everyday materialism which has become indispensable for navigating in today’s myth-cloaked cybersphere. A good enough reason for us to catch up with them.
 Julian Oliver & Danja Vasiliev – “Deep Sweep” (2015); Photo by JULIAN OLIVER, BENGT SJÖLEN AND DANJA VASILIEV
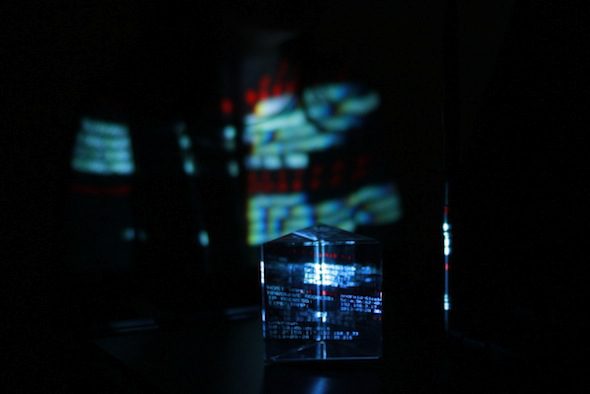
Julian Oliver & Danja Vasiliev – “Deep Sweep” (2015); Photo by JULIAN OLIVER, BENGT SJÖLEN AND DANJA VASILIEV Julian Oliver – “Binary Operations: Stuxnet” (2012); Courtesy of the artist
Julian Oliver – “Binary Operations: Stuxnet” (2012); Courtesy of the artist
Nicolas Hausdorf: To start off, how did you access the Stuxnet virus? Was it difficult?
Julian Oliver: In fact it only took me a couple of hours to find it. Plenty of seedy forums linked to archives that claimed to contain Stuxnet but none had a checksum matching that of the ‘official’ Stuxnet found in the wild. After looking through about a dozen downloads in a jailed virtual machine I finally found it on a university server, in a publicly readable directory of a security researcher. Madness.
NH: A lot of your art seems to be about rendering visible possibilities of everyday technologies in ways that highlight the full amount of their invasiveness. Is this your artistic project?
JO & DV: In part, yes. However it’s not the invasiveness of a given technology that is the core concern for us but the implicit trust so much of us are prepared to place in it, without examination. This has especially been the case with computer networking and the many consumer devices that use it – trust that is then routinely abused by governments and corporations alike. To this end, we’re interested in encouraging a ‘healthy paranoia’, one that may lead to critically engaging works of engineering that at the outset appear to be black-boxes, or otherwise just bafflingly complex.
There could perhaps be no better example than the so-called Cloud, which for many years we’ve warned about in lectures and workshops (a concern was central to our 2009 ‘Men In Grey’ project (“We are the Lightning in an Age of Cloud Computing”)).
While the Cloud is better described as other people’s computers, the popularised image of a harmless bundle of steam, deterritorialised and intangible, supports a dangerous myth from something that is very much geographical, political and material. It is children’s book metaphors such as these that remove any interface for critical engagement and debate, so much so that 51% of Americans were found in a survey to believe that bad weather affects cloud computing – a fact we mention often in our talks.
 Julian Oliver & Danja Vasiliev – “Men In Grey” (2011), Exhibition detail of quarantined M.I.G equipment, presented at Aksioma gallery, Ljubljana, Slovenia; Courtesy of the artists
Julian Oliver & Danja Vasiliev – “Men In Grey” (2011), Exhibition detail of quarantined M.I.G equipment, presented at Aksioma gallery, Ljubljana, Slovenia; Courtesy of the artists
NH: Your project ‘Newstweek’, and the possibility of altering information, reminded me a lot of the way your browser history and machine in general is sending information that can alter your search results. Can you tell us a bit more about the localised manipulation of information? What do you mean by your notion of browser-based reality?
JO & DV: ‘Newstweek’ grew from several different agendas and technical challenges but what has emerged as the primary trope of the project is to interrupt the implicit belief that what occurs in the browser is a direct reflection of what is hosted on the server. It literally demonstrates that there are almost always many computers along the route and that s/he that controls the route ultimately has control of the content.
Traditionally, ‘Newstweek’ implements a man-in-the-middle attack by changing the topology of the local network such that all traffic passes through the device. This enables the owner of a ‘Newstweek’ device to go anywhere in the world and change the news read on that local network, making that network a ‘reality island’, but only if the content is unencrypted. Still baffling for us is that almost 5 years after ‘Newstweek’ almost all news sites are still serving HTTP and not HTTPS, with perhaps The Intercept to be the first to truly present a ‘trusted’ – in the technical sense – online news service. Wikipedia, which names itself an encyclopedia, only switched to HTTPS-by-default last week.
 Julian Oliver & Danja Vasiliev – “Newstweek” (2011), flyer; courtesy of the artists
Julian Oliver & Danja Vasiliev – “Newstweek” (2011), flyer; courtesy of the artists
NH: Mesh networks are increasingly being used in social Arab Spring-type movements (and are developed with US State Department money). What do you think of the potential and limits of such technologies?
JO & DV: End-to-end encrypted mesh-networks have plenty of potential, especially in crowd/protest situations. While there’s been plenty of productive hype around city-wide mesh-networking projects today, it’s important to recognise there’s already a long history of community-run offline networks, often using roof-mounted ‘cantennas’ and other improvised antenna infrastructure to give coverage. There’s perhaps no better example than Melbourne Wireless, which is well over 10 years old and still going strong. Looking to such early efforts we can learn a lot about the limitations and challenges of city-wide meshes: factors like zoning regulations, FCC (U.S) regulations as to EM radiation and the challenge that property presents DIY antenna infrastructure (we often don’t own the roof of the building we live in).
NH: Do you think there can be an “off the grid” in the smart city of the future?
JO & DV: Without the ability to legally roll out our own infrastructure in so many cities we have little choice but to re-purpose (some would say “reclaim”) existing infrastructure. It’s important to mention here that the Internet never “belonged to the people” and so in that sense there’s no Internet to “take back”. Almost all wide-area network infrastructure is completely privatised, from the submarine cables to the optic fibre running under our pavements.
Rather than seeing this as taking a cynical position, however, it offers a clear and lucid starting point for finding new ways to increase our freedom of movement while upholding and asserting precisely the same basic rights we enjoy in the street. To that end, encrypted layers, networks-within-networks (like that of VPNs and Tor) are precisely the direction we ought to be going.
 Julian Oliver – “Transparency Grenade” (2014); Photo by Khuong Bismuth, courtesy of the artist
Julian Oliver – “Transparency Grenade” (2014); Photo by Khuong Bismuth, courtesy of the artist
NH: What is the ‘Transparency Grenade’? Has it been applied? How do you think power has adapted to the practices of leaking?
JO: I certainly wouldn’t tell you if I had deployed TG, even if I had! The ‘Transparency Grenade’ uses well-known techniques to capture data in its surroundings and as such you can be sure that attempts to harvest secrets/volatile information ‘in the air’ are widely practiced.
If by “power” you mean corporate and/or governmental powers, then there has been quite a rapid adaptation to the craze over leaks. Since the so-called Snowden Revelations markets have boomed for reducing the attack-surface of critical communications infrastructure and data storage. This has meant increased demand for Penetration Testers (pentesters), server hardening services, security auditors and the overhauling of security policies. Disk encryption on employee laptops is probably a lot more popular now, as are virtual private networks and encrypted calls in the enterprise or government.
NH: Your work ‘PRISM: the Beacon Frame’ appears to have laid open some sort of cognitive dissonance between technological reality, practice and popular acceptance of it? Why do you think people get angry at your works when they merely reflect a technological reality?
JO & DV: In fact PRISM was widely appreciated by far more people than were disturbed by it. Over 740 people at the main ArtHackDay part of the Transmediale 2014 exhibition received SMSs on the opening night without us knowing their phone numbers. Many screenshots quickly made their way to Twitter, Facebook, blogs etc. A couple of German politicians expressed their appreciation of it, especially as it was clearly pointing to the American interception of GSM communications at the Bundestag. Of all those people there were just a few that took offense that we had (playfully) demonstrated an innate vulnerability of their trusty mobile device and that was enough to have the head of the AV team cut our Base Station down and quarantine it, threatening to call the federal police if we re-installed it.
To answer your last question, expressing anger when you feel you’ve been ‘tricked’ is common. It’s where that anger is directed that is especially interesting for us; many would rather find the artists/Critical Engineers to be the tricksters rather than the mobile phone manufactures and service providers that have, not once, warned them that it can happen. This is the difference between a person choosing to grow from such an encounter and a person choosing to remain unchanged as a result, coveting and/or identifying with their ignorance.
 Julian Oliver and Danja Vasiliev – “PRISM: The Beacon Frame” (2013), Transmediale 2014 ArtHackDay; Courtesy of the artists
Julian Oliver and Danja Vasiliev – “PRISM: The Beacon Frame” (2013), Transmediale 2014 ArtHackDay; Courtesy of the artists
NH: Can you explain your conception of critical engineering and the task of the critical engineer?
JO & DV: Critical Engineering was born from a shared frustration that we three authors of the manifesto felt with the frame of Media Art. As so much of our work was concerned with critically engaging engineering directly – as a set of ideologies, technical traditions, aesthetic and political cultures – we decided to re-cast our practice as Critical Engineering. Simply put, we felt Engineering is far too important – a reach touching all areas of modern life -that it can’t be left to science and industry alone. Rather, engineering must be engaged outside of an obligation to utility such that it can be explored with plasticity and criticality.
The manifesto came quite easily to us and was soon voluntarily translated into 15 languages by excellent people the world over. We’re very fortunate to find it now taught/studied in many universities world wide, alongside finding it on the walls of hack-labs and so-called maker-spaces.
NH: How can I become a critical engineer? Where do I start?
JO & DV: Take a technology upon which you depend (there are many) and ask yourself if you understand how it works and if not, why not? Note the thresholds and supposed barriers between you and reaching understanding (warranties? laws? physical challenges?). Take your curiosity, healthy paranoia and problem-solving skills to that challenge, reading what you need to read, finding or building the tools you need. Whether you succeed or fail publish your results as a project, a manual or both.
Many people that we think are excellent Critical Engineers received no formal training.
NH: Do you think Berlin has become some sort of hub for cyber dissidents? How can this function be enhanced and protected?
JO & DV: Berlin has certainly become quite a hub and it’s no wonder. There isn’t another Western capital that leaves you alone – and there are many ways and places to hide in Berlin. It also has a strong and well-developed cypherpunk and crypto-anarchist community (world-class tech-support for dissidents).
Who knows how long this will all last, after all, you only have to look at the size of the new BND, Germany’s own huge spy organisation. They need a lot of employees. Berlin’s so-called hacker-scene could become pretty paranoid in the years to come.
 Julian Oliver & Danja Vasiliev – “Deep Sweep” (2015); Photo by JULIAN OLIVER, BENGT SJÖLEN AND DANJA VASILIEV
Julian Oliver & Danja Vasiliev – “Deep Sweep” (2015); Photo by JULIAN OLIVER, BENGT SJÖLEN AND DANJA VASILIEV
NH: Whats currently interesting you? What are you working on?
JO & DV: Several projects, as usual! First off, we’re about to launch a balloon containing wide-spectrum RF equipment all the way to the edge of space – the first civilian reading of the RF space between the ground and the stratosphere. We’re particularly interested in the commercial and military UAV/Drone space and as such need to get between them and the satellite infrastructure they talk to. It’s all pretty unknown up there.
The project is called ‘Deep Sweep’, and began as part of a residency at Center for Creative Inquiry (Pittsburgh). Intended as a low-cost platform, we’ll release a full guide for others to study the skies above their homes.
___________________________________________________________________________________
Nicolas Hausdorf is an essayist, theorist and black-magician of the social sciences. He has written for Vice, Offline Samizdat, Arena magazine and Cobra Res. His book “Superstructural Berlin” (with Alexander Goller) has been published with Zero Books.